Trusted By Enterprises Worldwide
Overlooked Attack Surfaces
Unaddressed Software Supply Chain Security Risks Leave Companies Open to Compromise

March 2026
axios Compromised on npm
Supply Chain Attack
Hijacked maintainer account used to publish poisoned axios releases injecting a hidden dependency that drops a cross-platform remote access trojan on install. attack

March 2026
Trivy Compromised
Malicious trivy-action exfiltrated CI/CD secrets to an attacker-controlled domain for 12 hours. A fake trivy binary release was also published to GitHub Releases.

March 2025
tj-actions/changed-files action is compromised
Application Security
Learn how StepSecurity Harden-Runner detected the tj-actions/changed-files supply chain attack






Complete SDLC Protection
The Definitive Platform for Software Supply Chain Protection
Complete SDLC Protection
The Definitive Platform for
Software Supply Chain Protection
GitHub Actions
CI/CD pipelines have privileged access to production secrets and infrastructure. StepSecurity provides runtime protection with Harden-Runner, a secure internal marketplace for GitHub Actions, and automated remediation.
01
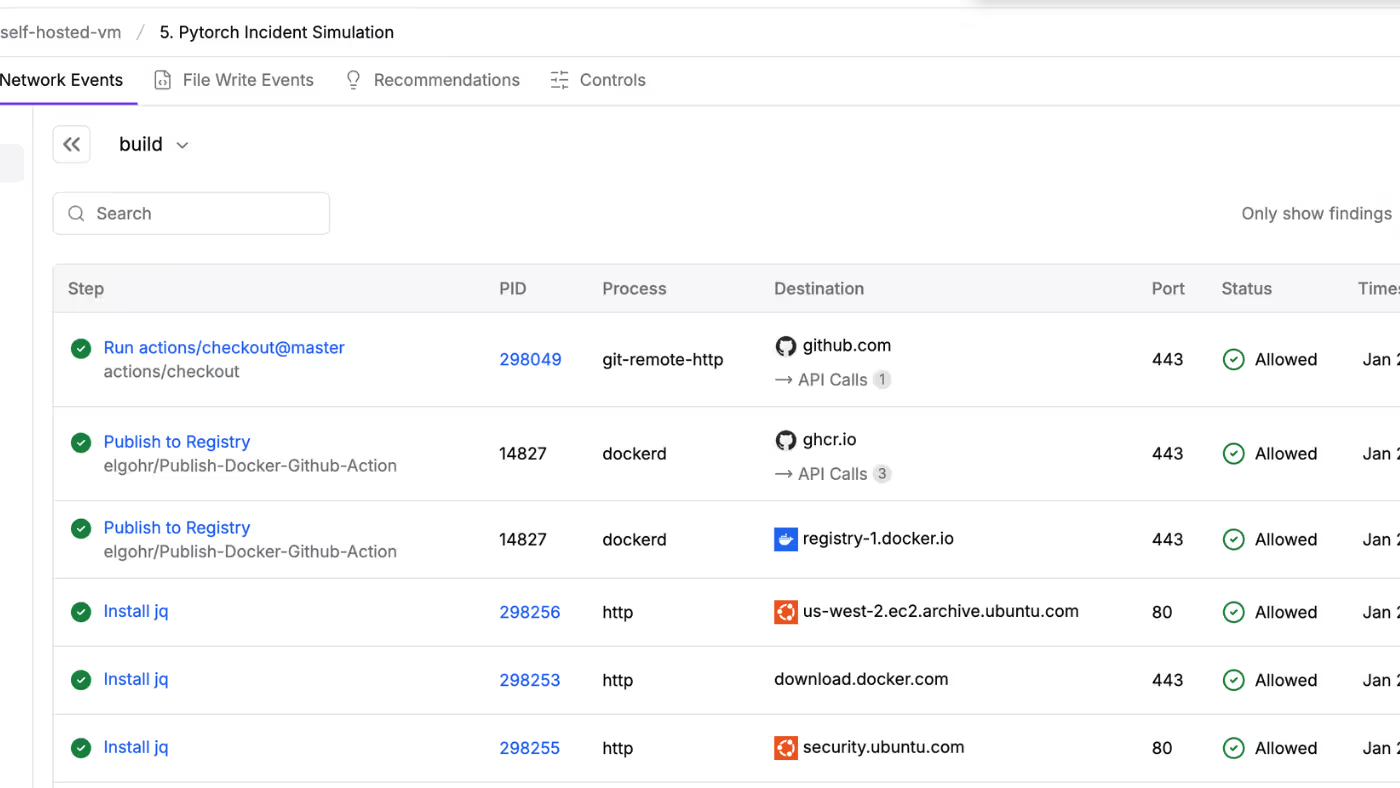
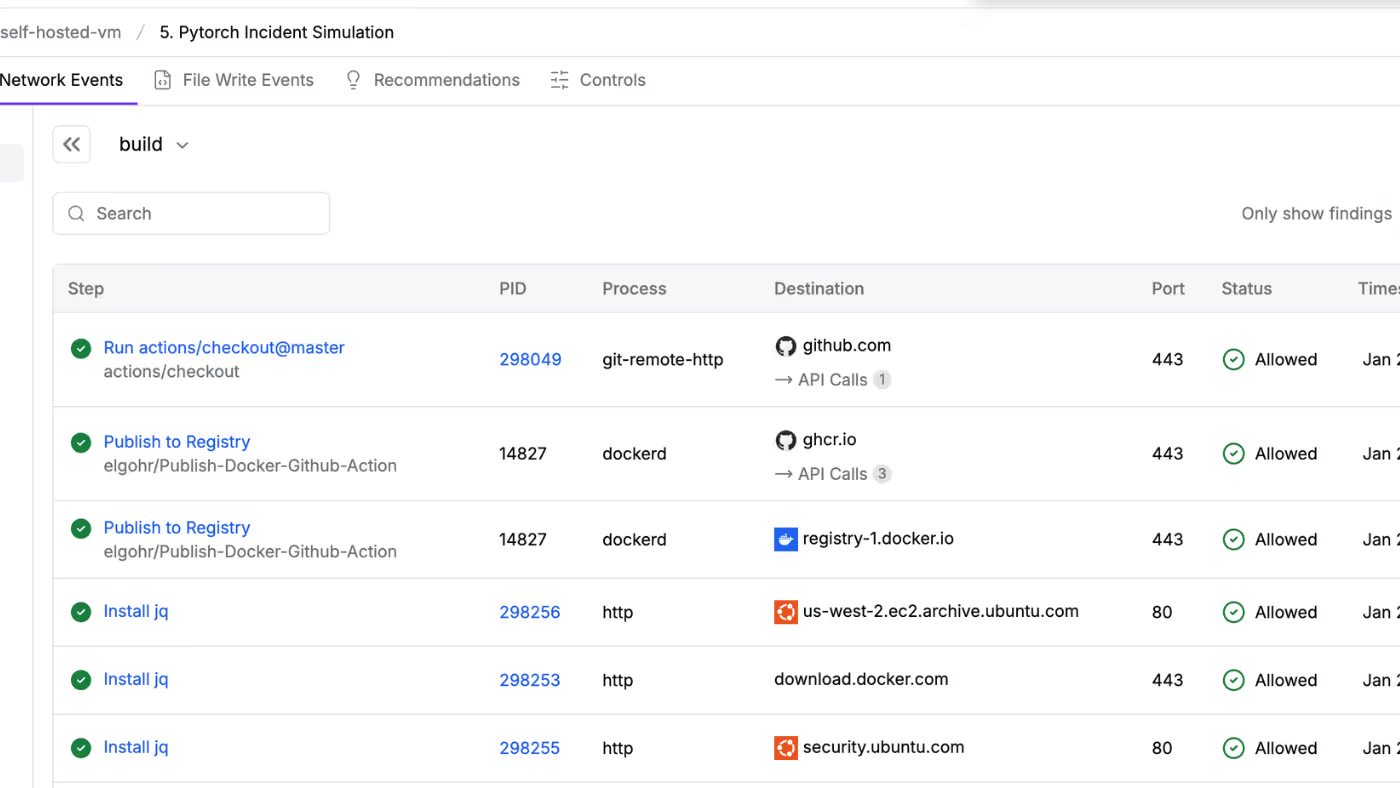
Runner Network Visibility
Gain full visibility into which job step initiated each network call, file write, or process execution. Contextualized runtime security insights correlated with each step of the workflow.
02
Anomaly Detection & Network Blocking
Automatically baseline network behavior for every job. Get alerted when a job makes a call outside its normal behavior - this is how the tj-actions breach was detected. Block unauthorized egress traffic.
03
Secure Internal GitHub Actions Marketplace
Build your own secure marketplace with StepSecurity Maintained Actions - drop-in replacements for third-party Actions that are hardened, verified, and actively maintained.
04
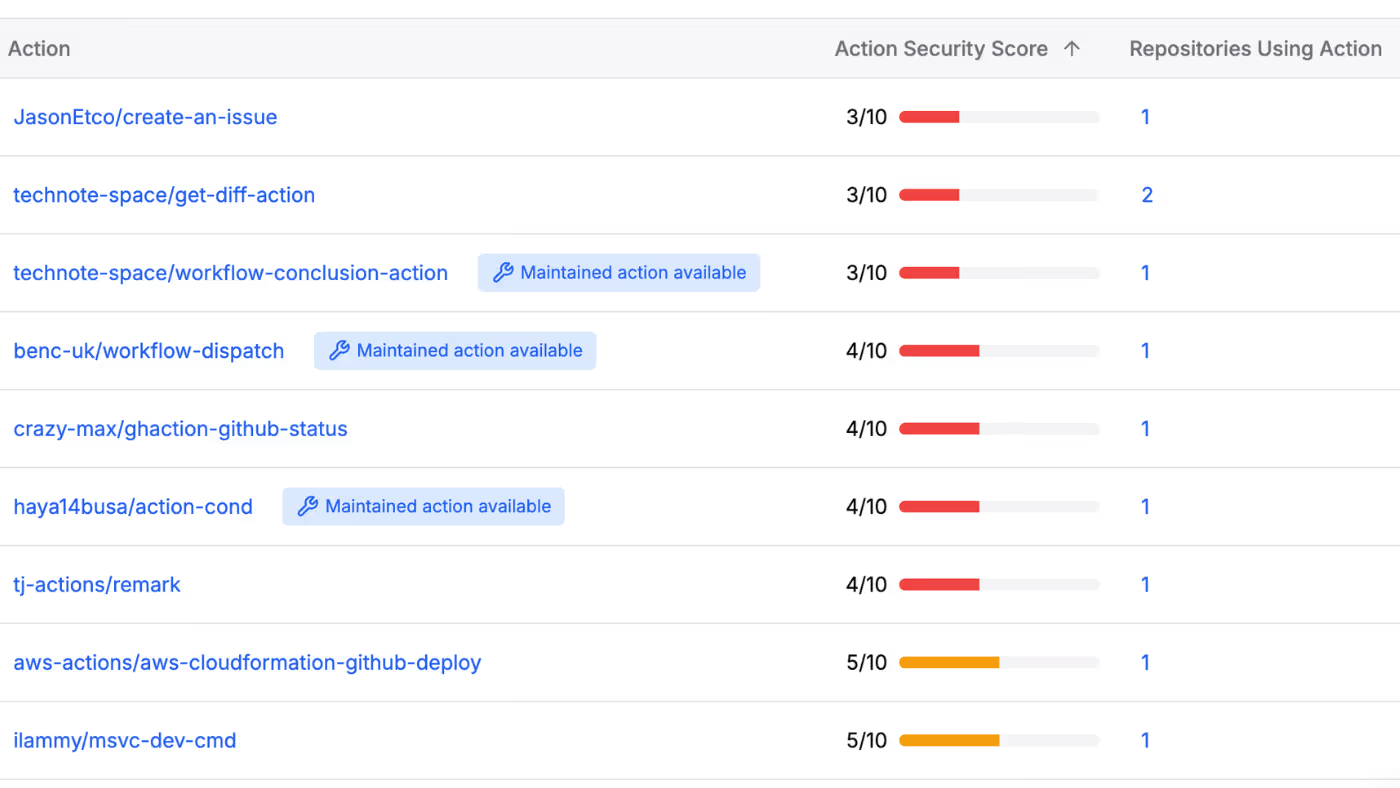
GitHub Actions Security Scoring
Know which Actions to trust. StepSecurity assigns a security score to third-party GitHub Actions - helping you choose safe, vetted options and track your entire Actions footprint across repositories.

05
Automated Security Remediation
Skip the YAML hassle. Automatically create pull requests to pin actions to commit SHAs, enforce least-privilege token permissions, and bring workflows in line with security best practices.
Dev Machine Guard
StepSecurity provides complete visibility and control over AI agents, IDE extensions, and dependencies.
01
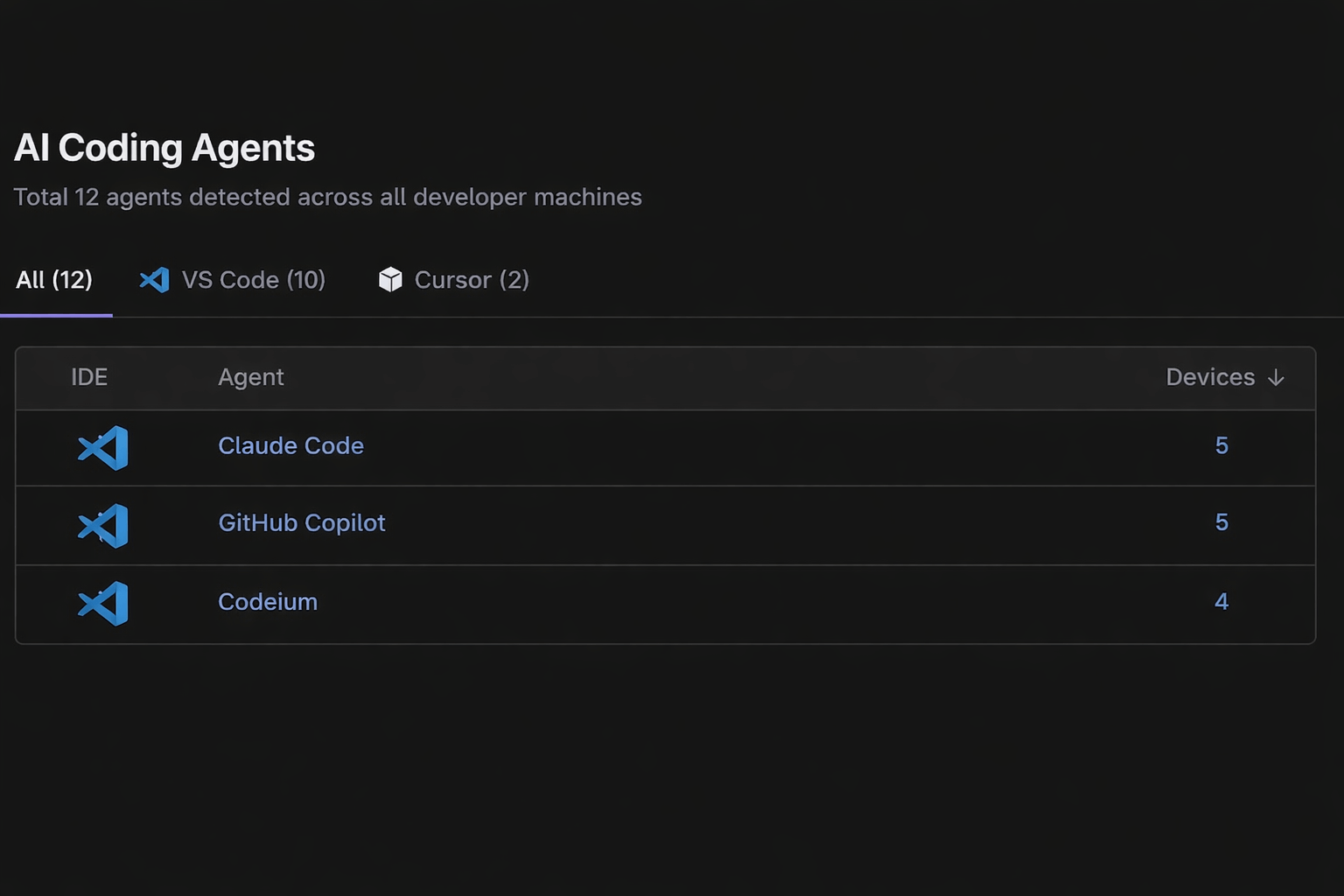
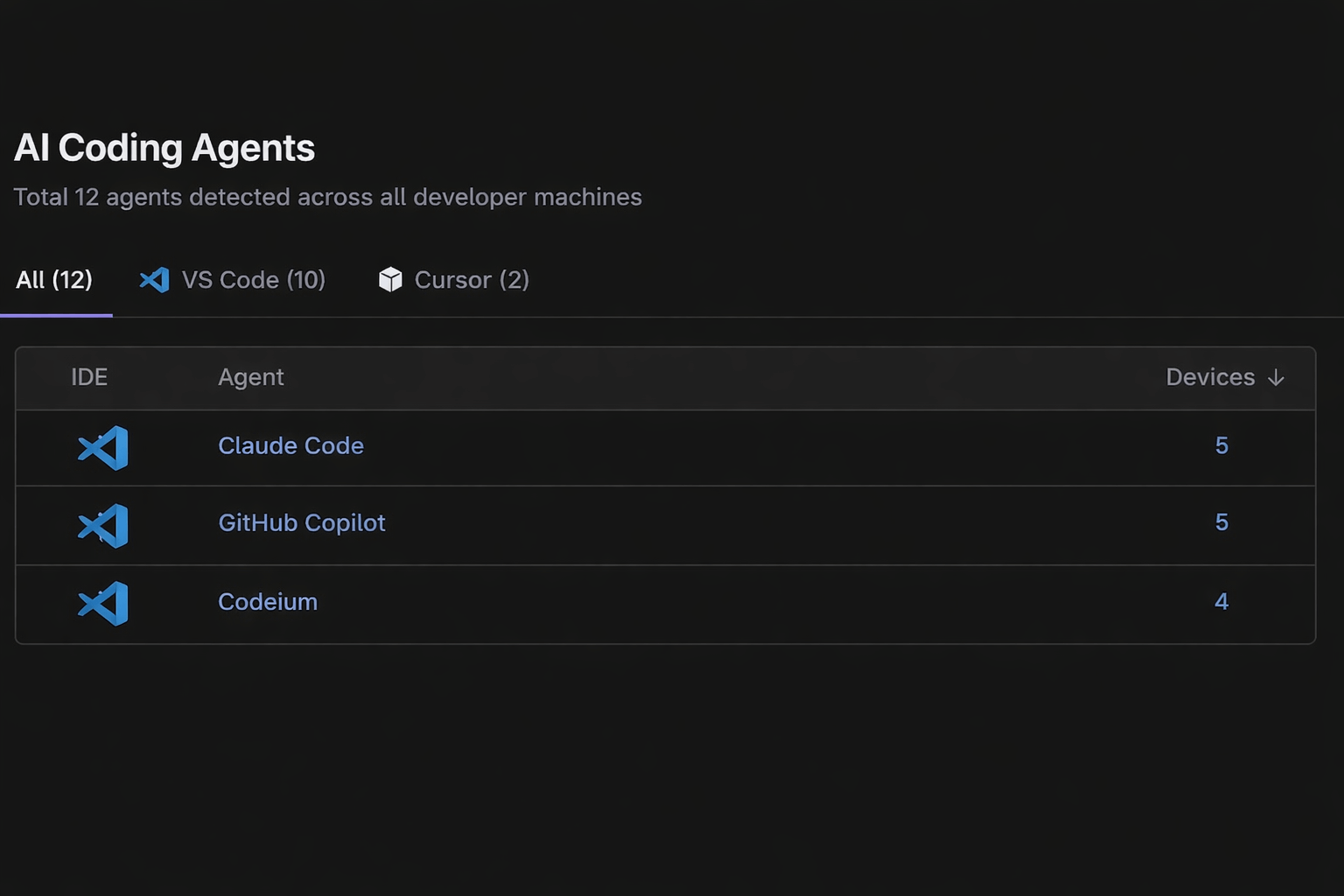
AI Coding Agent Inventory
StepSecurity provides complete visibility and control over AI agents, IDE extensions, and dependencies.
02
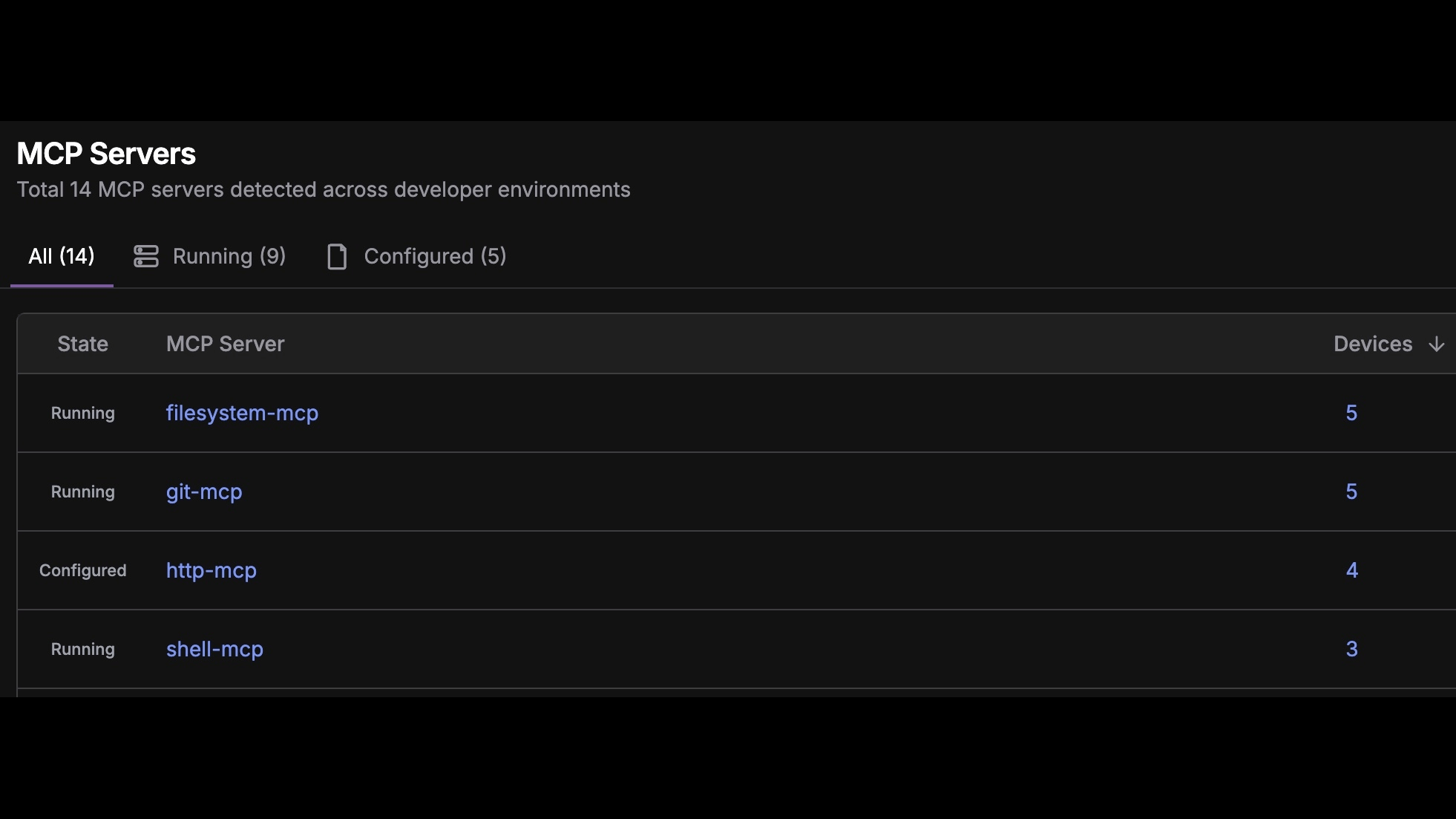
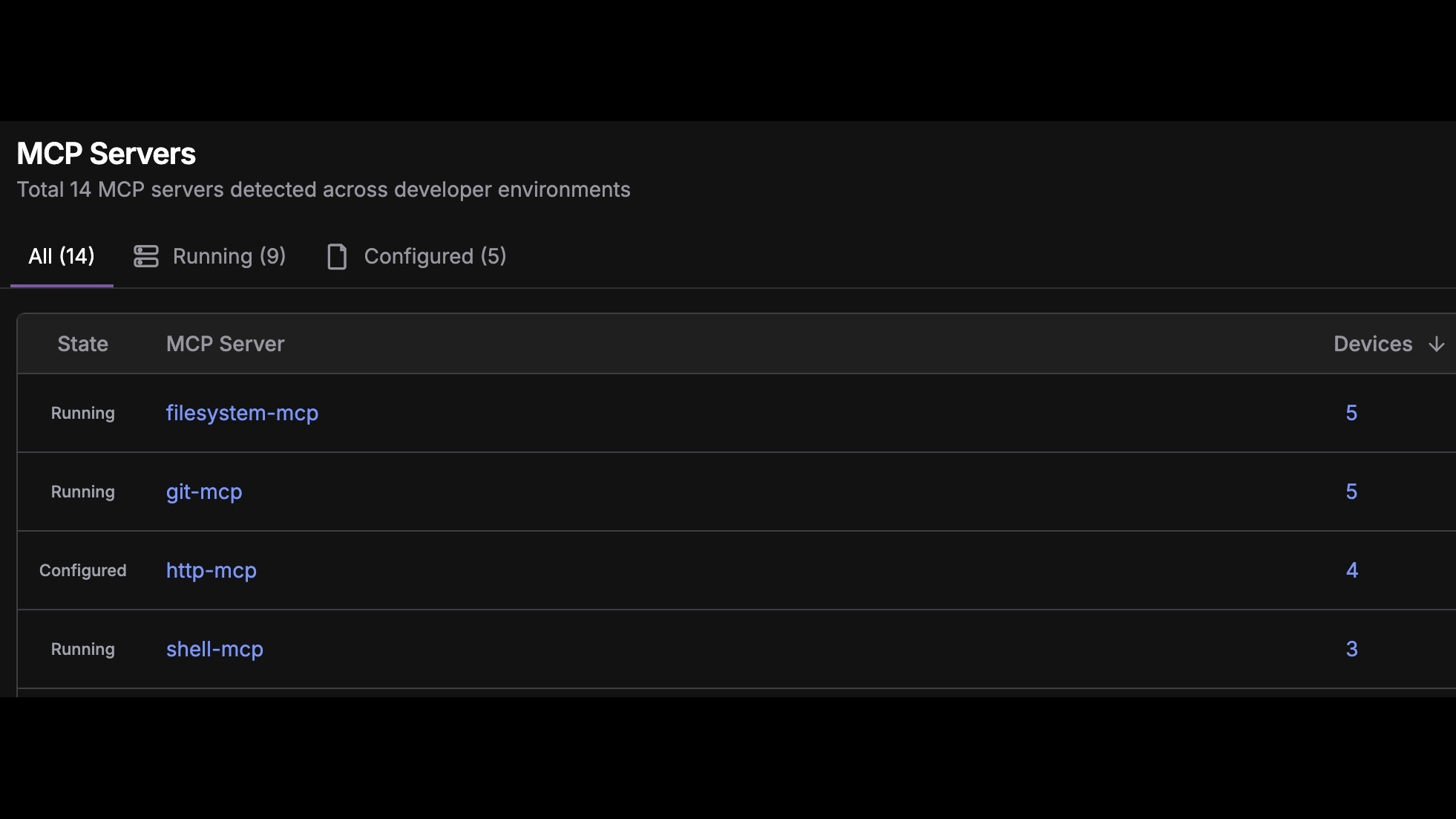
MCP Server Monitoring & Control
Gain visibility into Model Context Protocol servers connecting AI agents to your development tools.
03
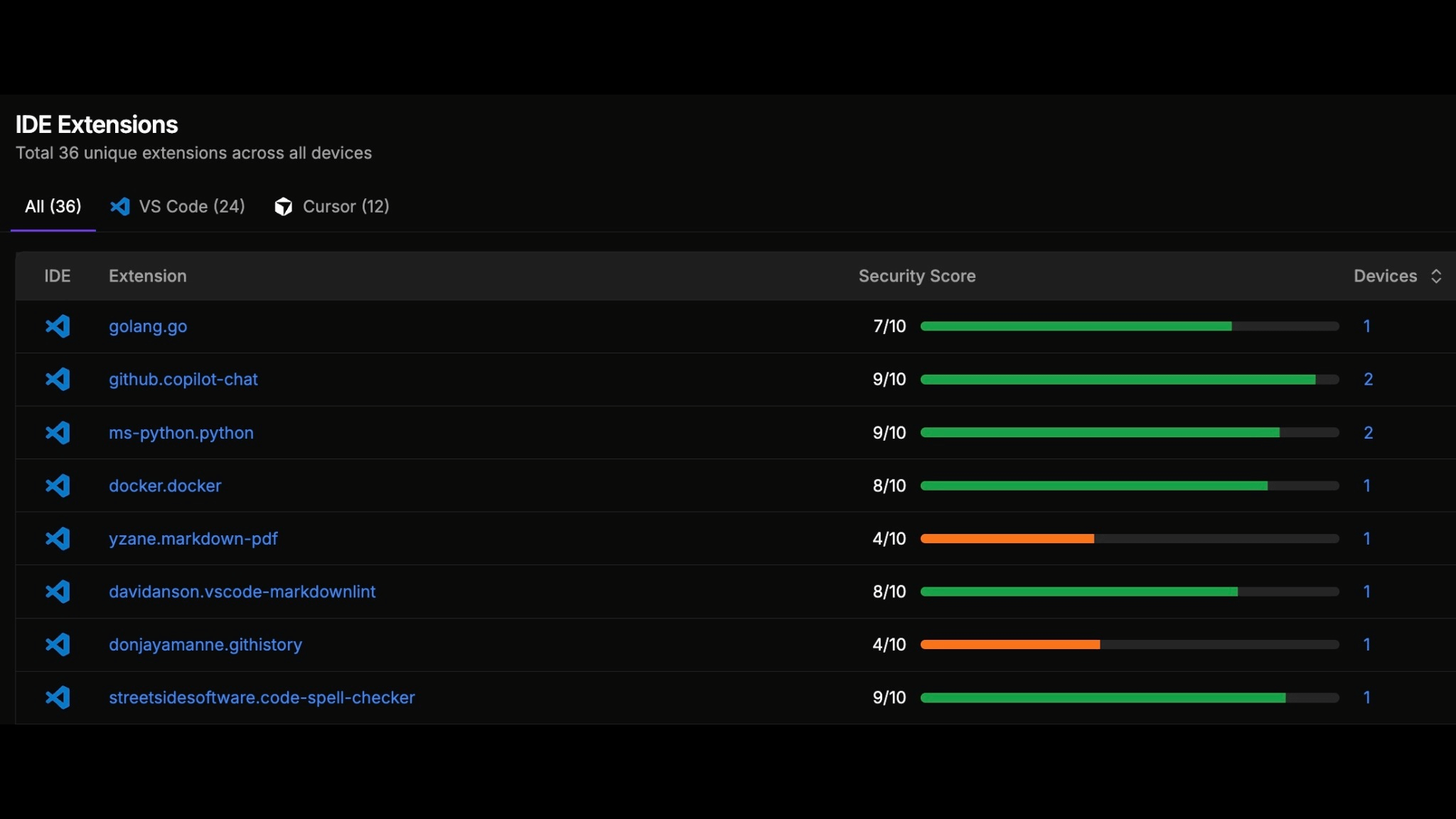
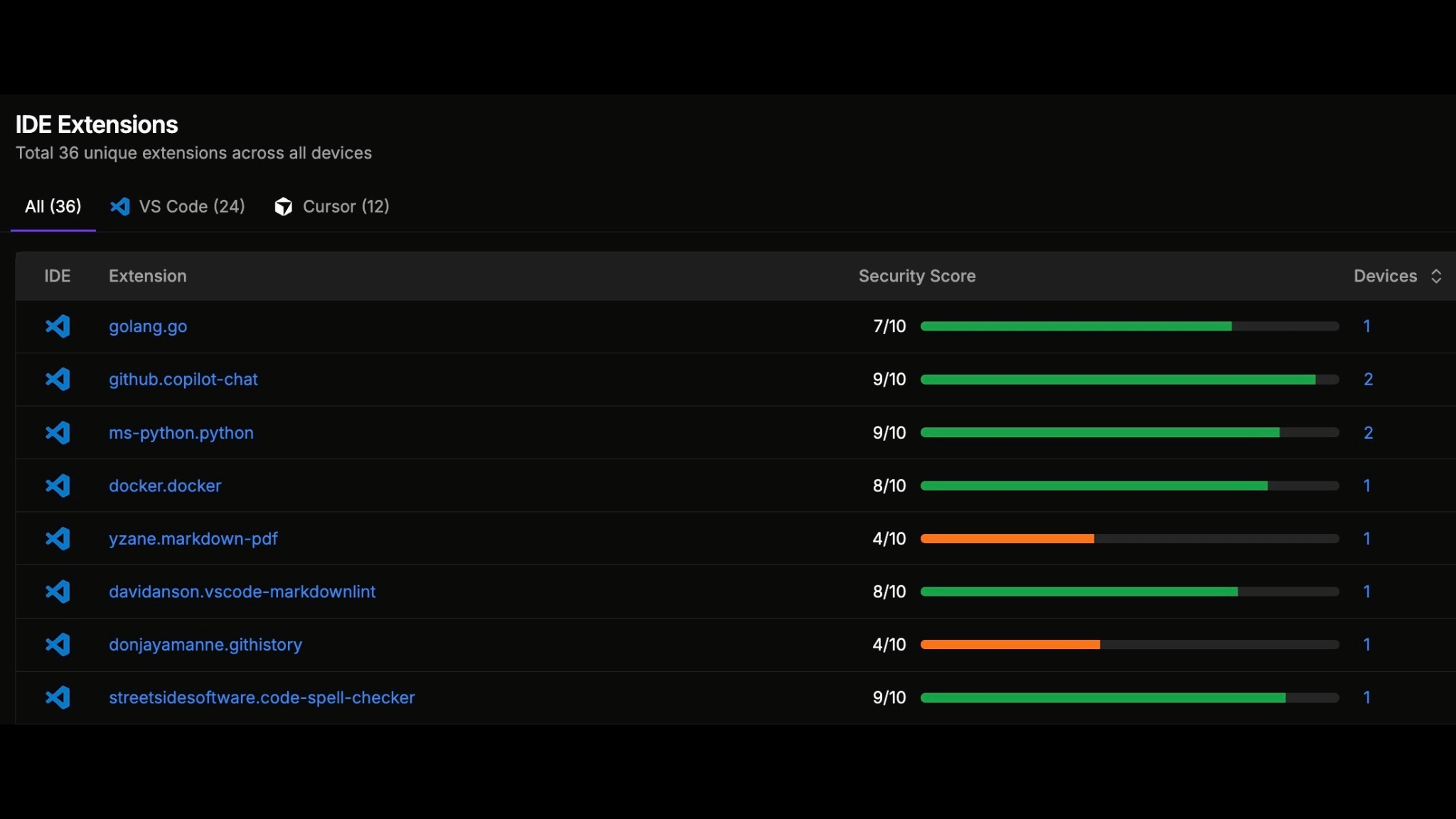
Complete IDE Extension Visibility
Track all installed extensions across VSCode, Cursor, JetBrains, and Windsurf IDEs organization-wide. Identify risky extensions before they compromise developer environment.
04
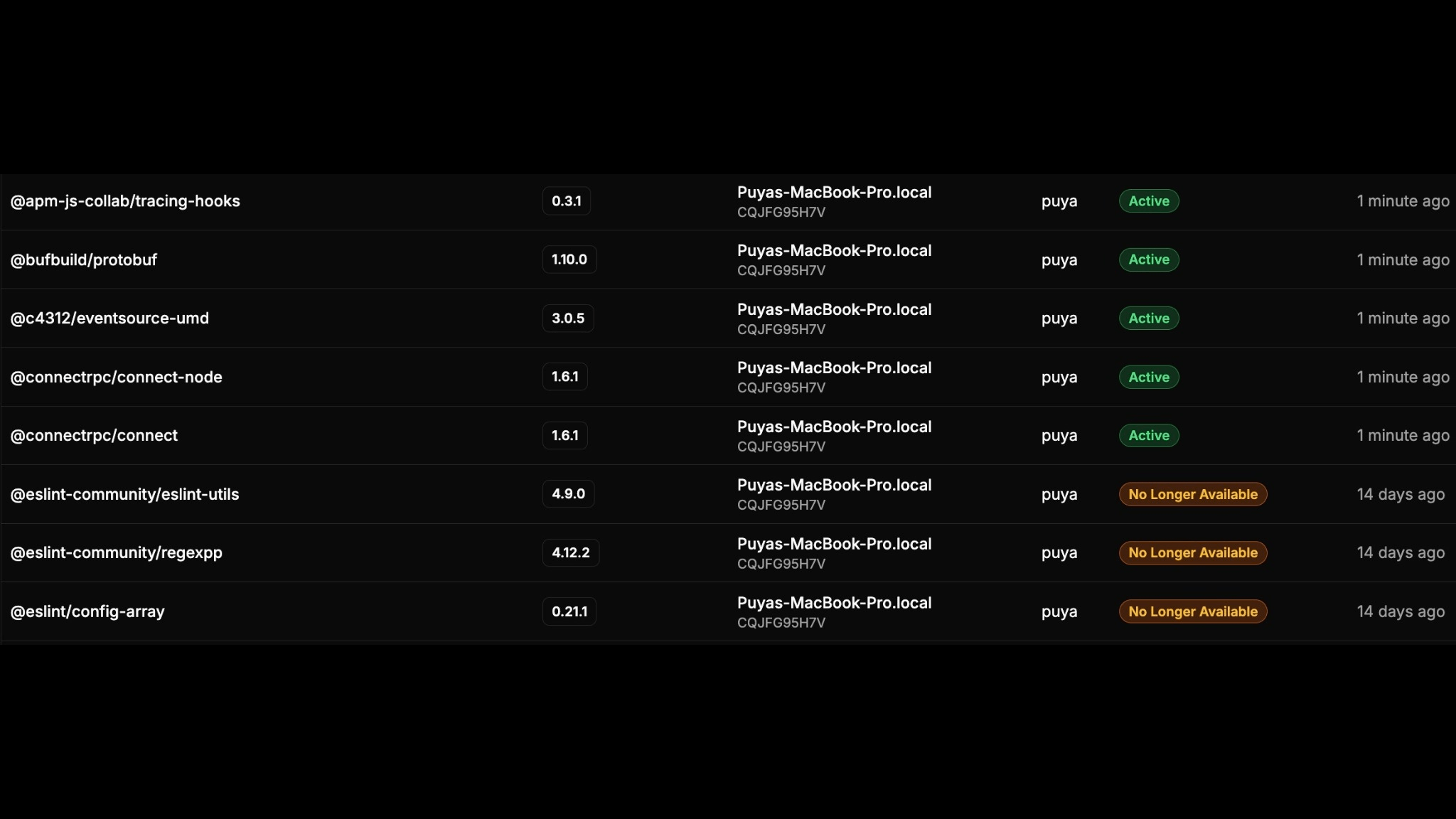
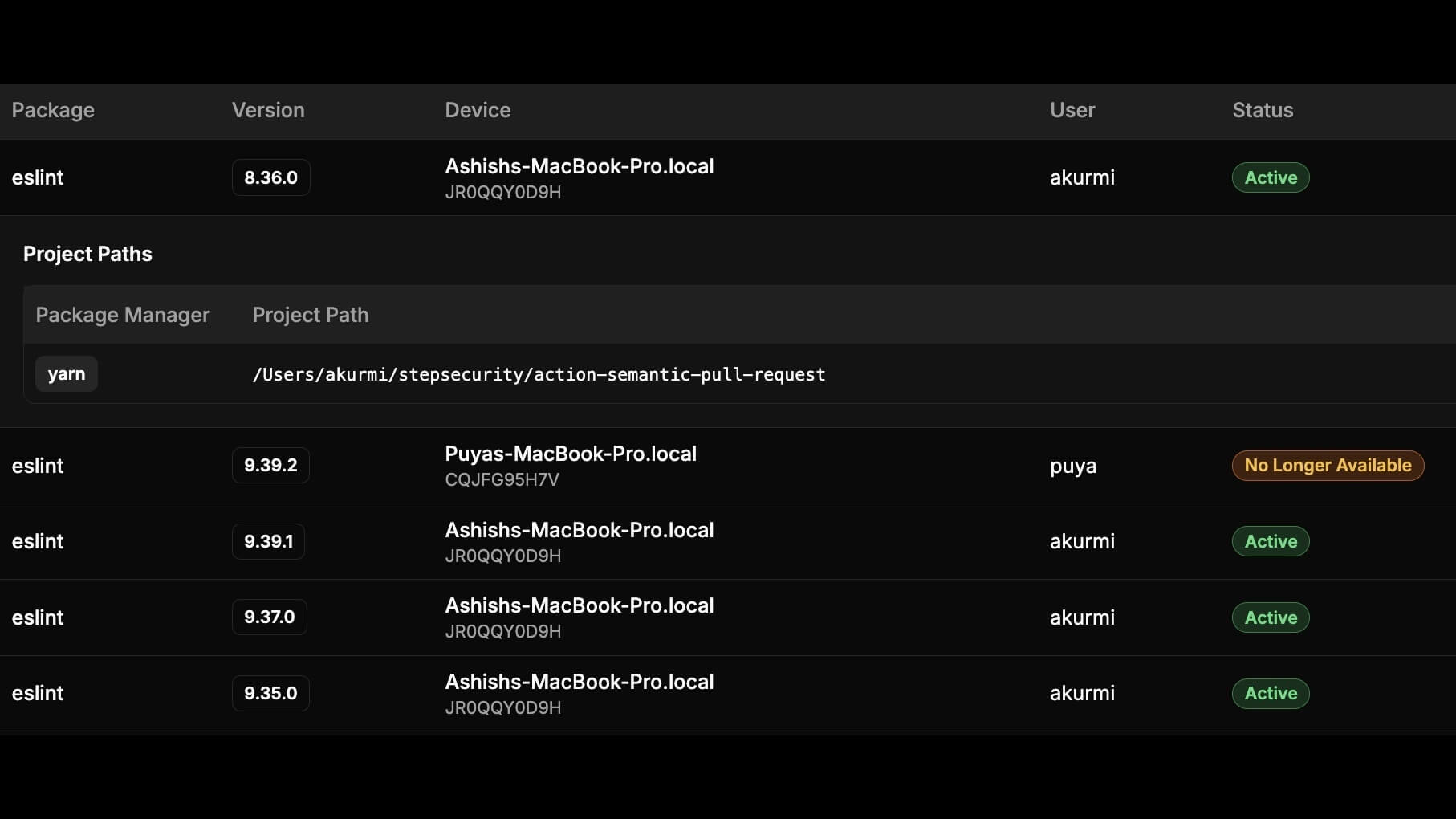
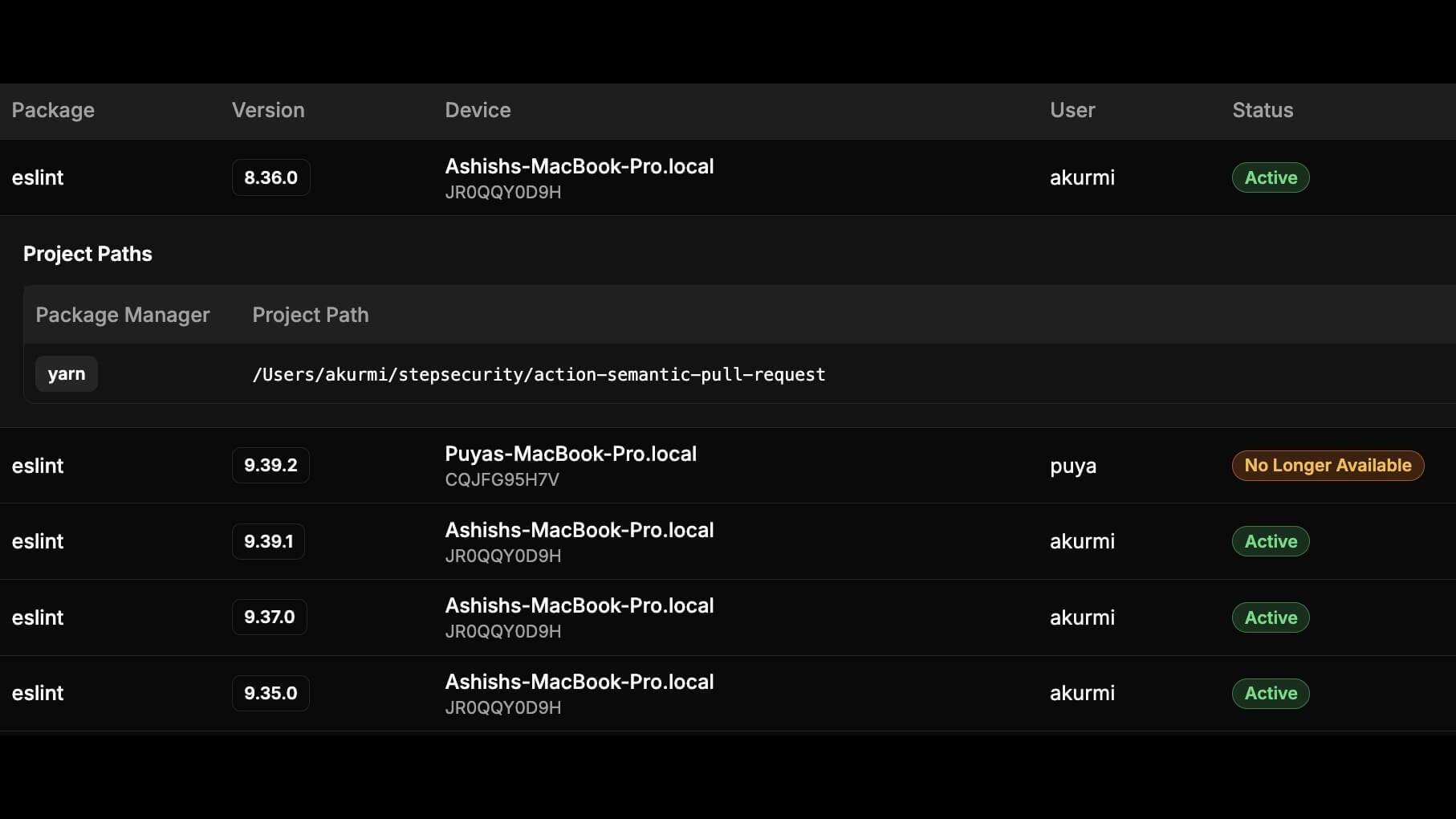
Dependency Monitoring
Monitor open-source packages installed on all developer machines. Detect compromised dependencies and automate the incident response process.
05
Allowlist & Cooldown Policies
Implement approved IDE extension and OSS package lists and automatic cooldown periods for new releases.

OSS Package Security
StepSecurity detects compromised OSS packages across your organization and prevents them from entering your codebase with proactive controls.
01
Cooldown Period for New Packages
Block newly published OSS packages for a configurable period. Most supply chain attacks exploit fresh packages before the community can review them - cooldown policies give you time to verify legitimacy.

02
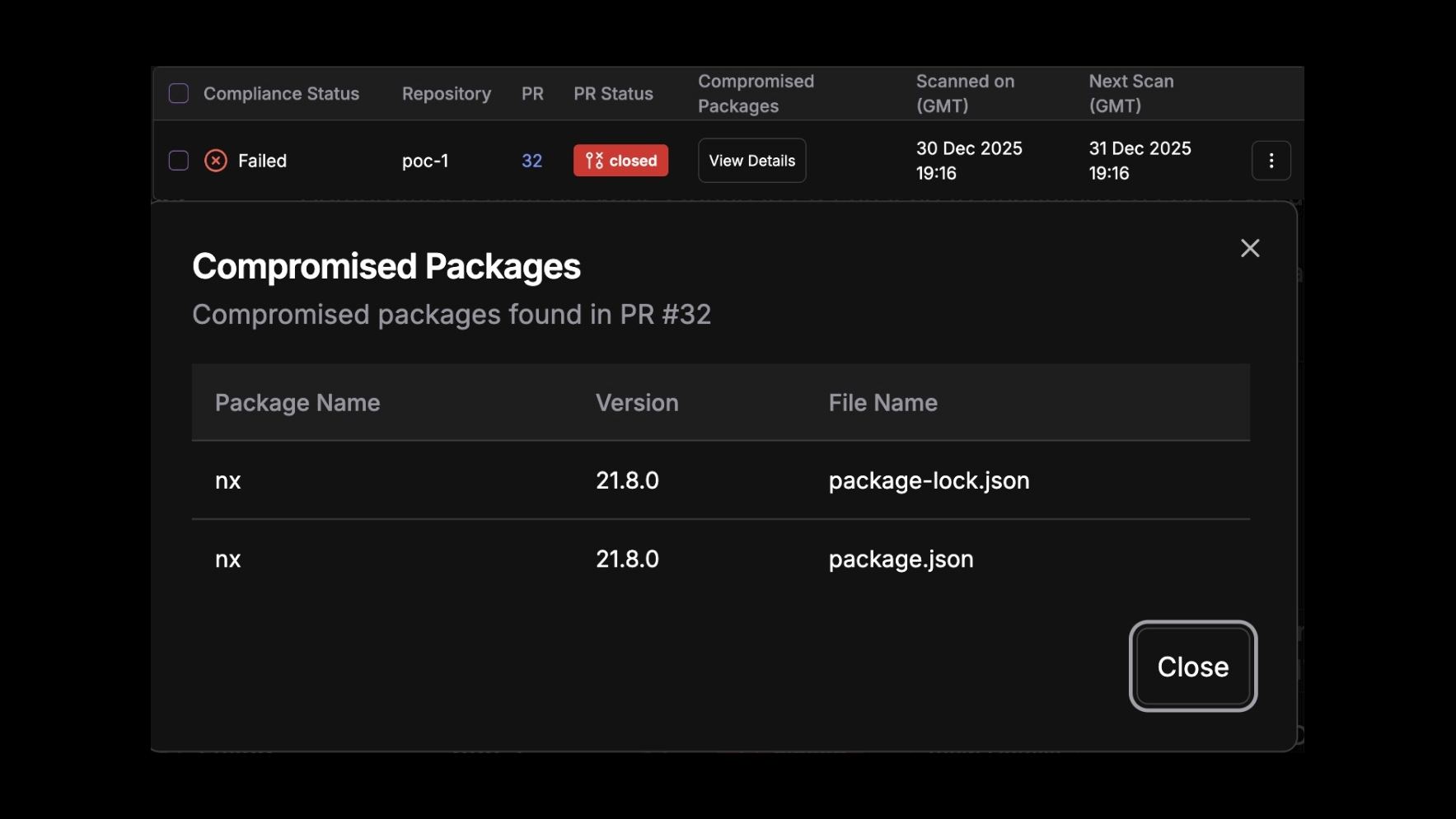
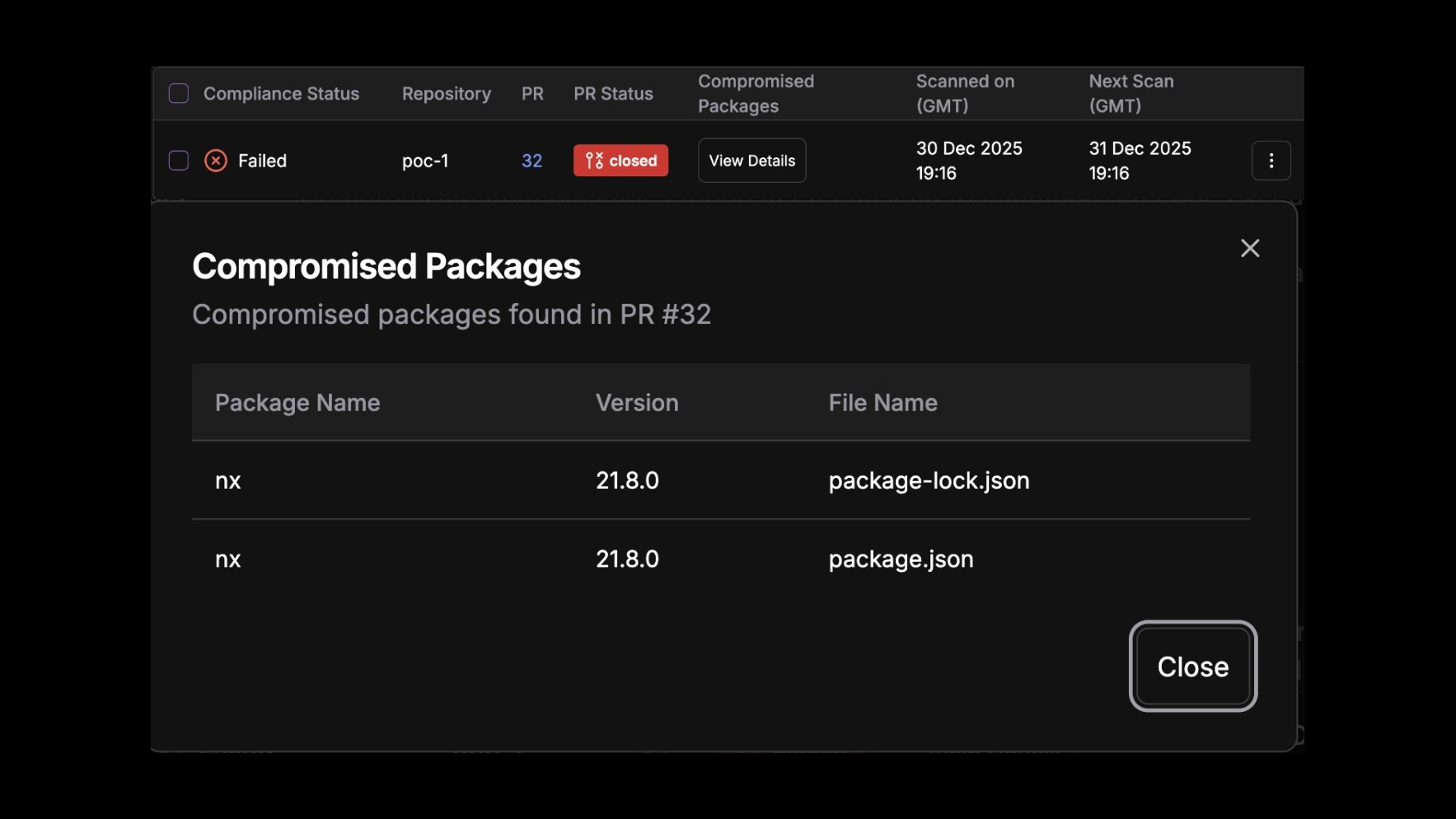
Compromised Package Detection in PRs
Automatically detect when pull requests introduce compromised OSS packages. Get instant alerts and detailed context on the threat, enabling your team to block malicious dependencies before merge.
03
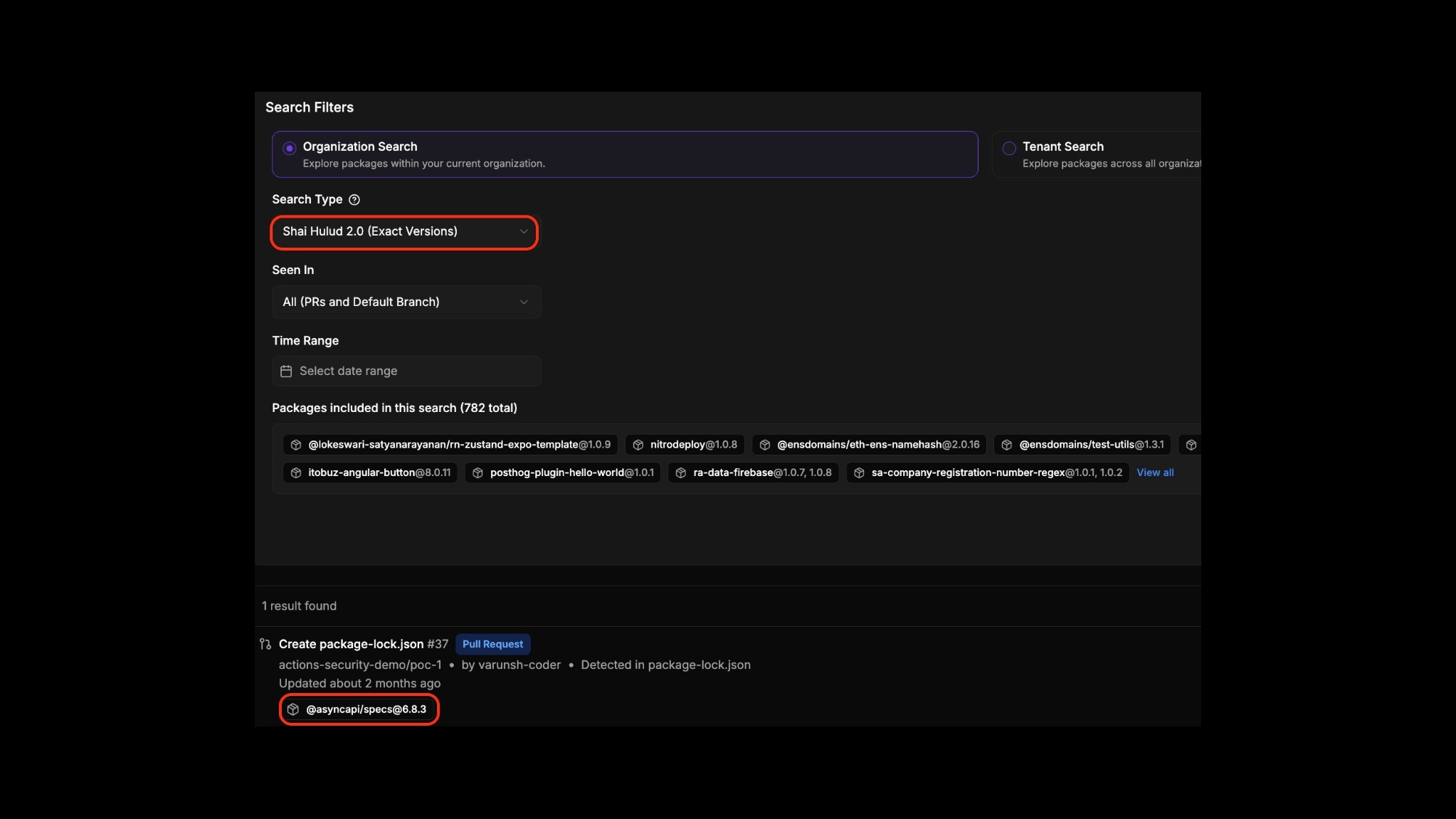
Enterprise-Wide Package Search
Instantly identify every instance of a specific OSS package across your organization including default branches, pull requests, and developer machines. Enable rapid assessment and response during supply chain incidents.
.png)
04
Historical Dependency Timeline
Track your dependency history over time to detect if you were vulnerable in the past. Even if a malicious package has been removed, understand your historical exposure window for incident response.
.png)
05
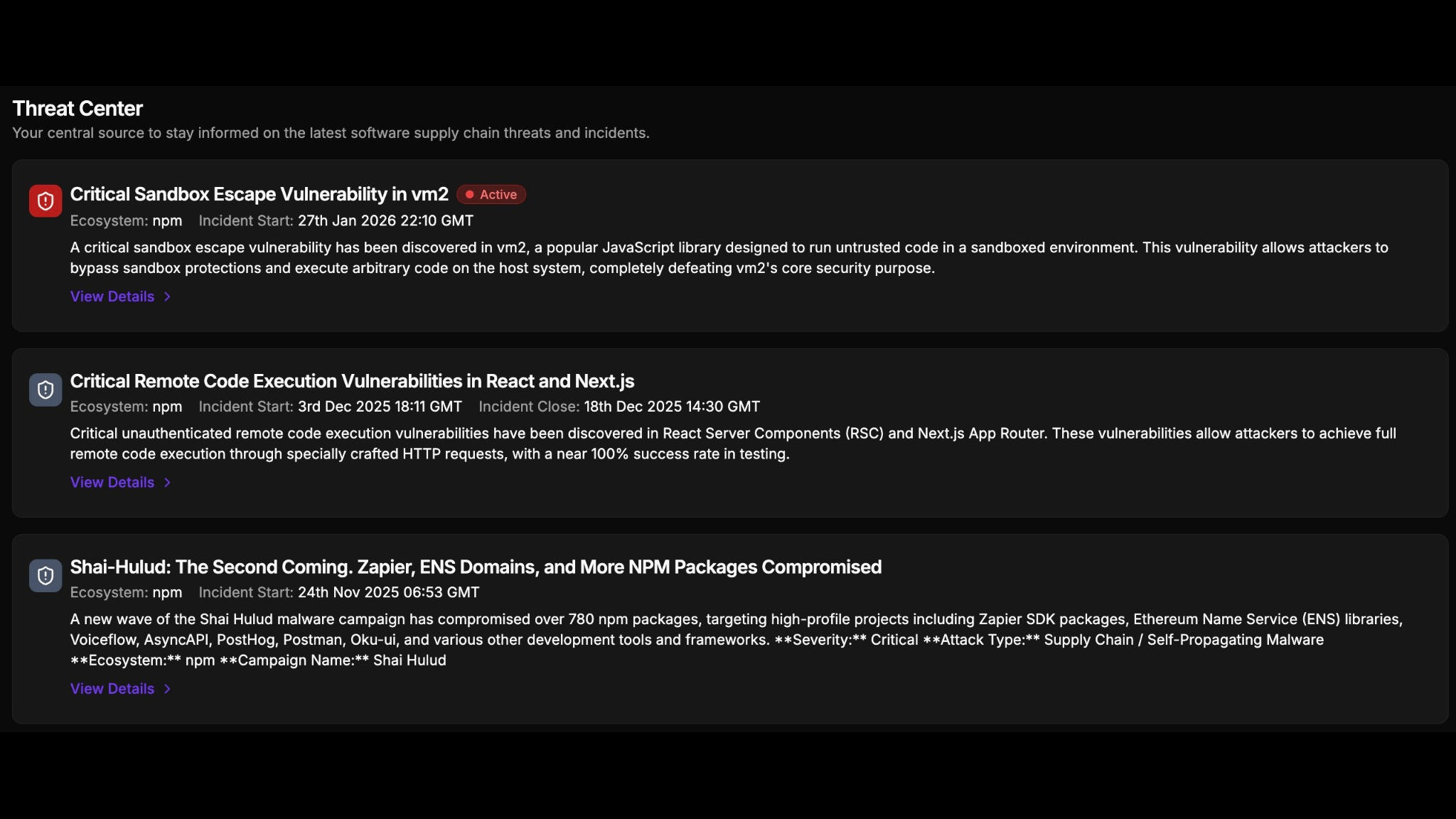
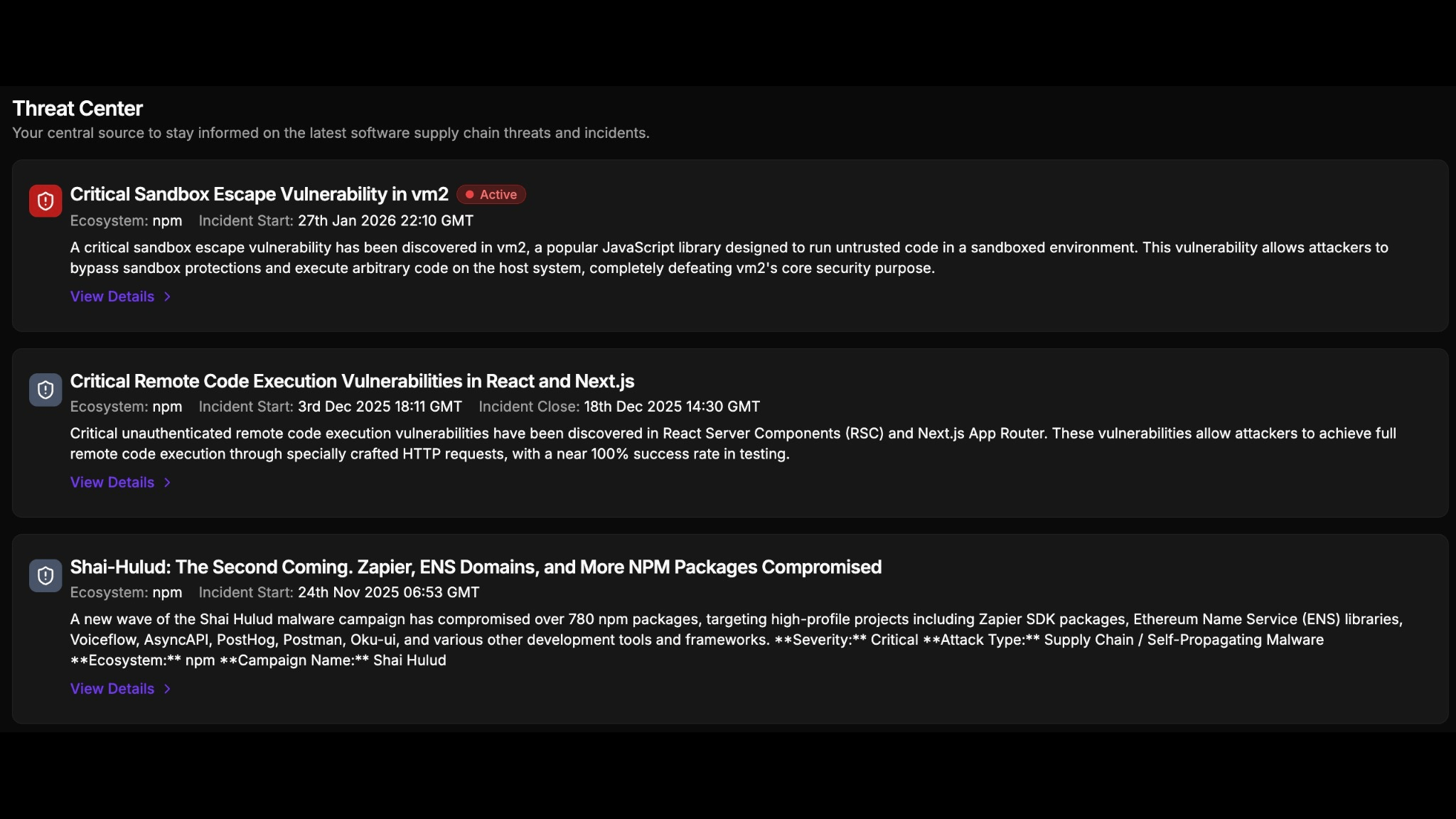
StepSecurity Threat Intelligence
Access real-time threat intelligence with detailed technical analysis, IOCs, and remediation guidance. Our research team is often first to detect major OSS supply chain attacks like Shai-Hulud and S1ngularity.


Why Step Security
Experience the StepSecurity Difference





















.png)