The data is in, and it validates the warnings StepSecurity has been sounding for years.
Datadog just released their State of DevSecOps 2026 report, analyzing tens of thousands of applications and their supply chain dependencies. The findings confirm a reality we've been documenting through real-world incident response: CI/CD pipelines and software supply chains remain dangerously underprotected, even as attackers increasingly target them.
We were invited to contribute our perspective to the report, and our co-founder Ashish Kurmi didn't hold back:
"GitHub Actions workflows routinely handle production credentials, generate release builds, and execute third-party code in highly privileged contexts, yet most organizations don't secure them with the same rigor they apply to production infrastructure. The major GitHub Actions compromises of 2025 made clear that attackers are systematically targeting this gap. Organizations need a first-principles approach to CI/CD security: understanding the blast radius of every workflow, monitoring runtime behavior, and treating build infrastructure as a high-value asset. That foundational thinking is what enabled early detection of attacks like tj-actions, Shai-Hulud, and s1ngularity, and it's what the industry needs to adopt broadly in 2026."
— Ashish Kurmi, Co-founder, StepSecurity
The report lays out five key facts about the state of DevSecOps. Every single one maps to a risk that StepSecurity's platform is purpose-built to mitigate. Here's how.
Fact 1: 87% of organizations have known exploitable vulnerabilities in deployed services
The risk: Datadog found that 87% of organizations have at least one exploitable vulnerability, affecting 40% of all services. Java services lead at 59%, followed by .NET at 47% and Rust at 40%. A key driver is outdated language and runtime versions: 10% of services run on at least one end-of-life (EOL) version, and when they do, 50% of those services have an exploitable vulnerability compared to 37% when no EOL versions are in use.
How StepSecurity mitigates this risk: Exploitable vulnerabilities don't just live in production code. They enter the software supply chain through compromised dependencies, outdated libraries, and insecure build processes. StepSecurity's Harden-Runner provides runtime security for GitHub Actions workflows by monitoring network traffic, file system activity, and process behavior during every CI/CD run. If a compromised dependency attempts to exfiltrate data or make unauthorized network calls during the build process, Harden-Runner detects and (with egress-policy: block enabled) prevents it.
This means even if a vulnerable or compromised library makes it into a dependency tree, StepSecurity can catch malicious behavior at the point where it matters most: during the build and deployment pipeline, before it ever reaches production.
Let’s walk through this interactive demo to see how Harden-Runner works:
Dev Machine Guard extends supply chain protection to developer machines, where the risk often starts before code ever reaches a pipeline. With Local npm Monitoring, security teams gain full visibility into packages installed on every developer workstation across the organization, enabling rapid identification of compromised dependencies before vulnerable code enters a repository or pipeline.
Fact 2: Dependencies are 278 days behind their latest major version
The risk: The median dependency is now 278 days behind its latest major version, up from 215 days last year. Java is the worst offender at 492 days behind, followed by Ruby at 357 days. Datadog's research also shows that older libraries carry significantly more vulnerabilities: libraries published in 2023 average 3.8 vulnerabilities per service compared to 1.3 for those published in 2025. Services deployed less than once per month have dependencies that are 70% more outdated than those deployed daily.
How StepSecurity mitigates this risk: Outdated dependencies are a ticking time bomb, and part of the reason teams fall behind is that they lack visibility into what's actually in their dependency tree and whether it's safe to update. StepSecurity tackles this from the supply chain angle:
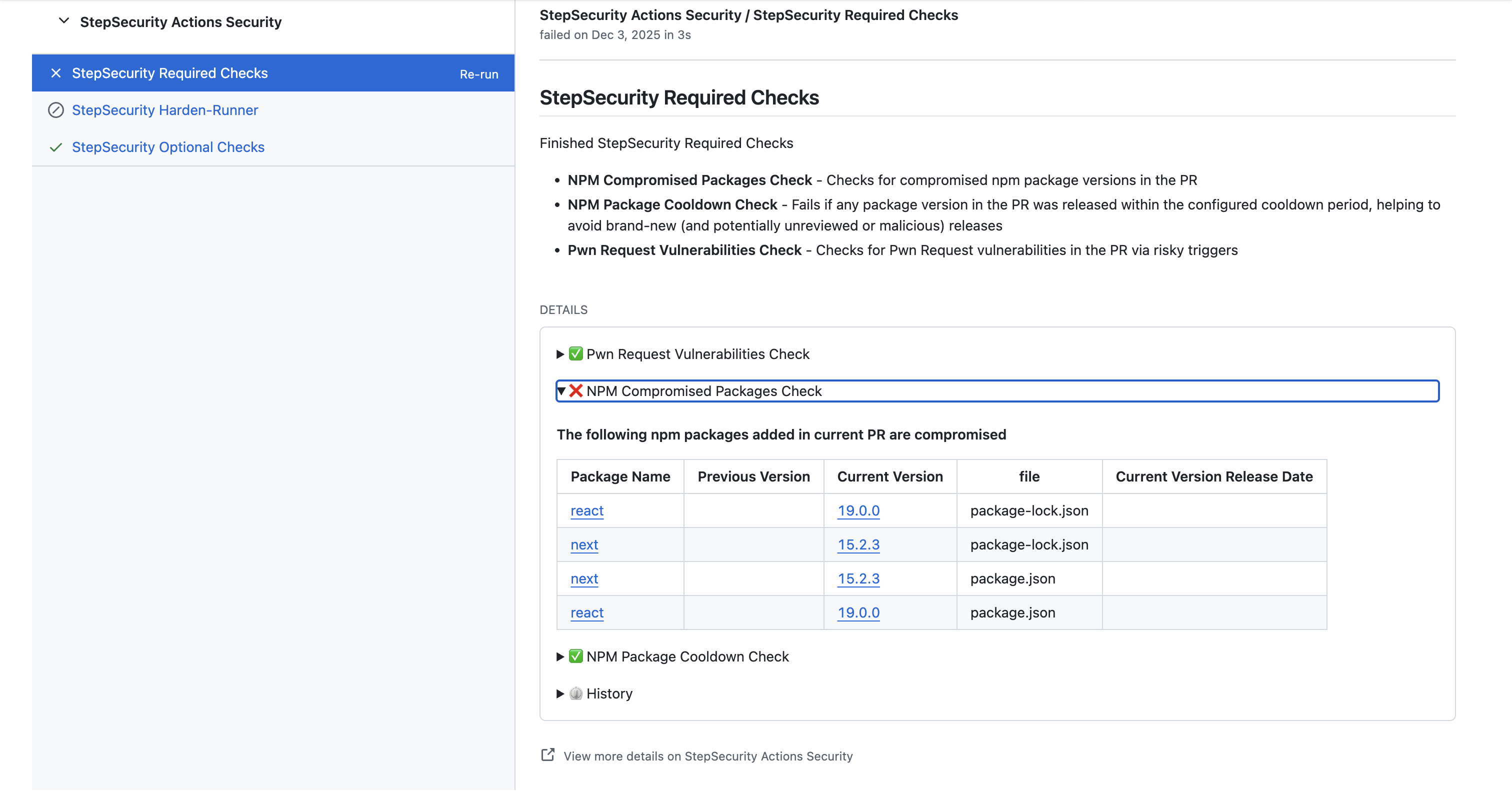
- NPM Package Compromised Updates runs as a GitHub Check on every pull request, ensuring that no dependency update introduces a package that is known to be compromised. StepSecurity maintains an internal database of compromised packages updated in real time, often before an official CVE is published. This gives teams the confidence to update more frequently, knowing that malicious versions will be caught automatically.
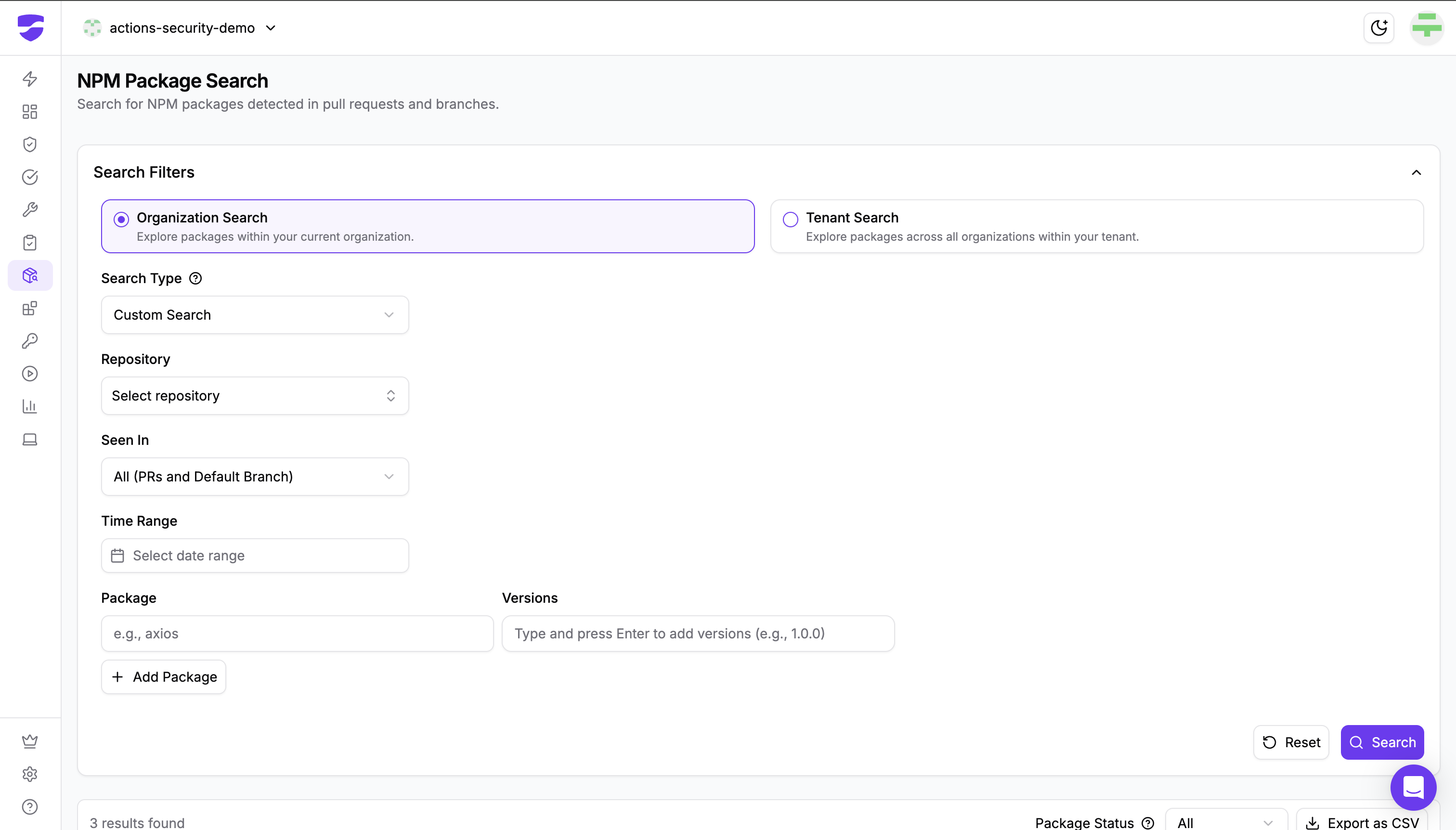
- NPM Package Search lets security teams search across their entire organization to identify where specific packages were introduced via pull requests. When a vulnerability is discovered in an older library version, this enables rapid identification of every affected repository so teams can prioritize updates where they matter most. Dev Machine Guard also plays a role here. Its NPM Package Search capability extends beyond repositories and pull requests to include developer machines, letting security teams identify where specific packages exist across the entire organization: in PRs, on default branches, and on local workstations. When an outdated dependency is found to contain a vulnerability, this complete visibility ensures no instance is missed during remediation.
- Artifact Monitor provides continuous compliance monitoring for your own published artifacts, verifying that every version is tied to a trusted CI/CD release process. This ensures that your internal packages don't become a source of supply chain risk for your own teams or downstream consumers.

By removing the fear that updating could introduce a compromised package, StepSecurity helps break the cycle of dependency neglect that Datadog's data exposes.
Fact 3: 50% of organizations use libraries within a day of release
The risk: While Fact 2 shows organizations are too slow to update, Fact 3 reveals the opposite extreme: 50% of organizations use third-party libraries within a day of release, 12% use public AMI images, and 32% use public Docker images less than one day after release. This is the exact window where supply chain attacks like Shai-Hulud and s1ngularity do their damage. Datadog notes that 1.6% of organizations using npm have used at least one malicious dependency in the past year, representing potentially tens of thousands of organizations that executed malicious code.
How StepSecurity mitigates this risk: This is the exact problem that our Artifact Security suite and GitHub Checks were designed to prevent:
- NPM Package Cooldown is a GitHub Check that automatically blocks any pull request that introduces a dependency published within a configurable waiting period (default: 2 days). If a PR tries to add a package that was published yesterday, the check fails automatically and passes on its own once the cooldown expires. No manual intervention required. Datadog recommends a one-week cooldown; StepSecurity lets you configure this to match your organization's risk tolerance. Since most supply chain attacks are discovered within the first 24 hours, even the default 2-day cooldown eliminates the vast majority of exposure.
- NPM Package Compromised Updates provides a second layer of defense by blocking any dependency that is already known to be malicious. During the Shai-Hulud attack, this capability automatically flagged pull requests attempting to pull in the compromised versions and blocked them from merging, shielding customers from the attack entirely.
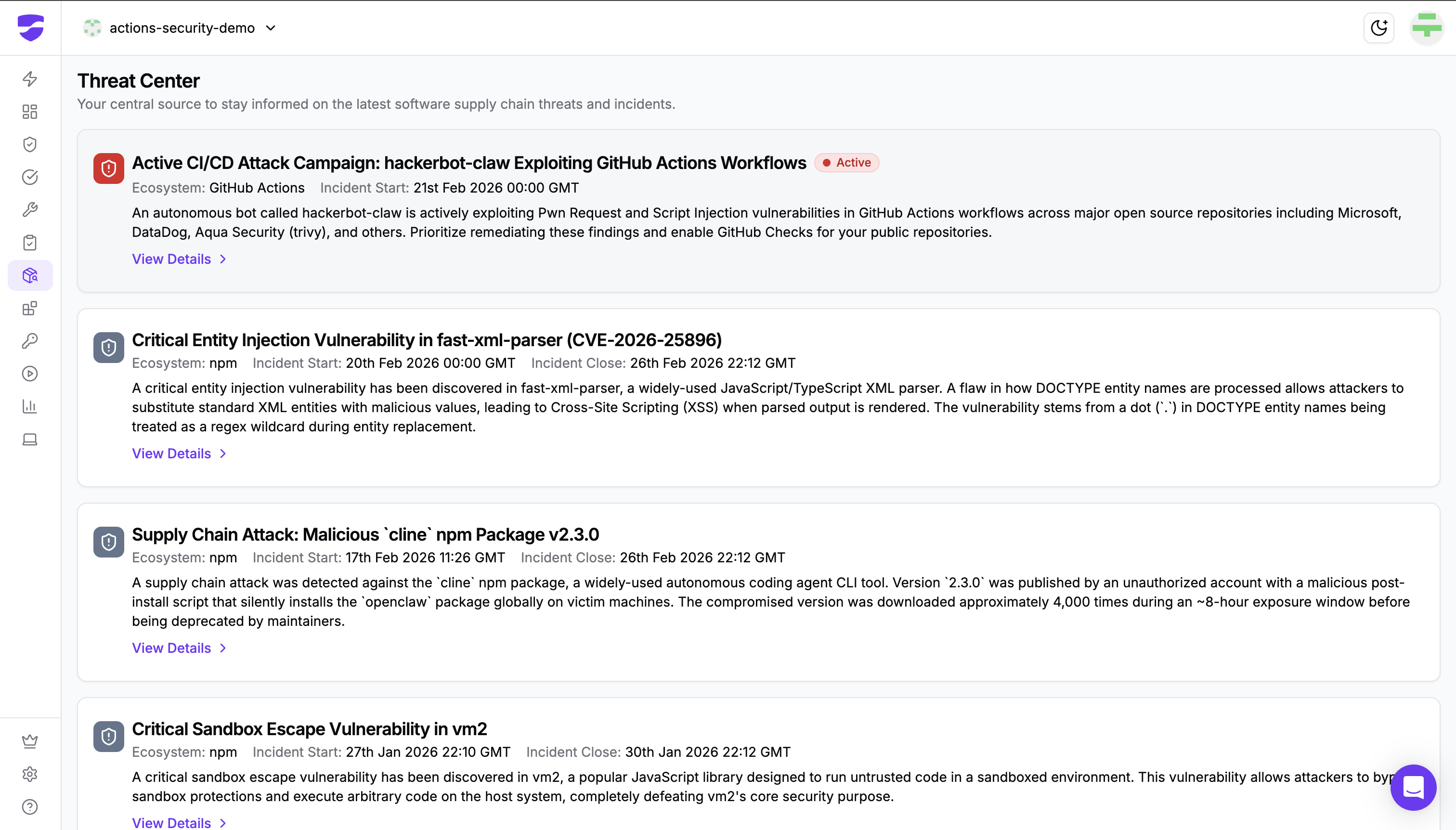
- Threat Center serves as a central hub for tracking active supply chain compromises across open-source ecosystems. When an incident like Shai-Hulud breaks, security teams can investigate details and apply remediation steps directly within the StepSecurity dashboard instead of scrambling across multiple sources.
- Harden-Runner provides the last line of defense at runtime. Even if a malicious package somehow enters a workflow, Harden-Runner detects anomalous behavior (unexpected network calls, unauthorized file access, secret exfiltration attempts) and can block it in real time. During the Shai-Hulud attack, Harden-Runner flagged the malicious behavior within minutes of publication, well before widespread exploitation began.
- Dev Machine Guard extends these protections to developer workstations. Local npm Package Monitoring tracks every package installed on developer machines across the organization, whether installed by a human or an AI coding agent, giving security teams full visibility into exposure when a compromised package is detected (like those in the Shai-Hulud campaign that targeted developer machines specifically). Dev Machine Guard's NPM Package Search also extends beyond repositories to include developer machines, letting security teams identify where specific packages exist across the entire organization (in PRs, on default branches, and on local workstations) for complete blast-radius assessment during incidents.
Together, these capabilities create a layered defense: cooldown prevents premature adoption, compromised package checks block known threats, and runtime monitoring catches anything that slips through.
Fact 4: GitHub Actions are left vulnerable to supply chain attacks
The risk: Every organization using GitHub Actions uses at least one marketplace action, but only 4% pin the hash for all marketplace actions. A staggering 71% never pin the hash for any of their actions. Worse, 80% of organizations use at least one third-party marketplace action not managed by GitHub and not pinned to a commit hash, and 2% are actively running previously compromised actions without pinning. The tj-actions/changed-files compromise demonstrated exactly how devastating this can be: attackers injected a malicious payload that caused affected repositories to write secrets to workflow logs.
How StepSecurity mitigates this risk: GitHub Actions security has been our core focus since day one, and we offer the most comprehensive solution in the industry for this exact problem:
- Orchestrate Security automatically pins GitHub Actions and container images to full-length commit SHAs across your repositories. This is the exact mitigation that both Datadog and GitHub recommend as the only way to prevent automatic updates to potentially compromised action versions. StepSecurity automates what 71% of organizations are currently failing to do manually.
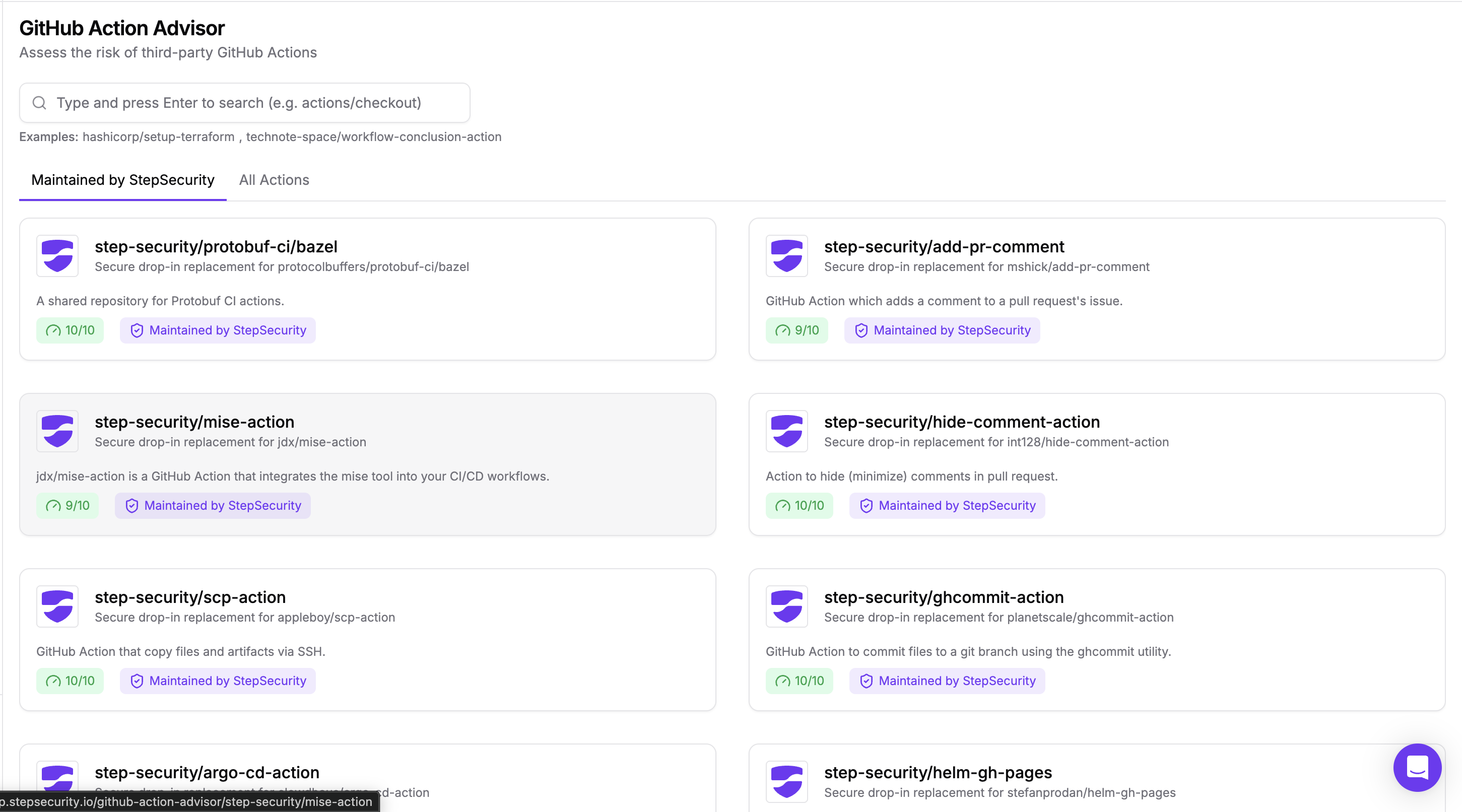
- StepSecurity Maintained Actions go a step further by providing curated, security-reviewed replacements for popular third-party actions. Every maintained action undergoes rigorous manual secure code review before onboarding, uses strict access controls with no persistent credentials, and has tag protection by default. This directly addresses the access control failures that enabled the tj-actions and reviewdog compromises. Enterprise customers can request onboarding of specific actions, and StepSecurity monitors upstream changes with defined SLAs for patching vulnerabilities.
- GitHub Checks include dedicated controls for PWN Request detection (catching insecure pull_request_target configurations that can be exploited by malicious forked PRs) and Script Injection scanning (flagging workflows that use unsanitized external inputs). These checks catch the workflow-level vulnerabilities that attackers exploit to gain initial access.
- Workflow Run Policies provide critical runtime controls for locking down which actions can execute in your environment. The Allowed Actions Policy lets you define an allowlist of approved GitHub Actions, ensuring only vetted actions can run across your organization. The Compromised Actions Policy automatically detects when a workflow attempts to use a known compromised action and cancels the run before it executes. For the 2% of organizations that Datadog found are still running compromised actions without pinning, these policies would immediately prevent those actions from executing.
Let’s walk through this interactive demo to see how Compromised Actions Policy works:
- Harden-Runner provides the runtime monitoring layer that detected the tj-actions compromise in real time. By monitoring network activity and restricting unexpected behaviors during workflow execution, Harden-Runner catches compromised actions even when they pass all static checks. This is how StepSecurity detected attacks against Google's Flank project and Microsoft's Azure Karpenter Provider in real time.
- Dev Machine Guard addresses the growing risk of AI-powered development workflows that interact with GitHub Actions. AI Agent Discovery automatically tracks all AI coding assistants (GitHub Copilot, Claude Code, Gemini CLI, and others) across your organization, and MCP Server Visibility monitors which Model Context Protocol servers are connecting AI agents to development tools, letting you prevent unapproved servers from being configured. As AI agents increasingly trigger and interact with GitHub Actions workflows, this visibility becomes essential to maintaining the security of your CI/CD environment.
The combination of automated pinning, maintained actions, workflow checks, and runtime monitoring means StepSecurity covers the full lifecycle of GitHub Actions security: prevention, detection, and response.
Fact 5: Most vulnerabilities should not page a human
The risk: Datadog found that only 18% of critical dependency vulnerabilities remain critical after adjusting severity scores with runtime context and CVE context. That means over 80% of "critical" alerts are effectively noise. The report also highlights that 98% of .NET dependency vulnerabilities are downgraded from critical, while 49% of PHP vulnerabilities stay critical. Over-prioritizing every vulnerability creates alert fatigue, diverts attention from real threats, and wastes developer time.
How StepSecurity mitigates this risk: Alert fatigue is a real problem, and it's compounded when security tools generate noise without context. StepSecurity's approach is built around actionable intelligence, not alert volume:
- Harden-Runner focuses on detecting actual malicious behavior at runtime rather than flagging every theoretical vulnerability. When a dependency makes an unexpected network call or attempts to access files it shouldn't, that's a high-signal alert that demands attention. This runtime context is exactly what Datadog describes as the key to reducing false positives.
- NPM Package Compromised Updates only blocks dependencies that are confirmed compromised, not every dependency with a CVE. StepSecurity's internal threat intelligence database is curated for accuracy, which means when a check fails, it's because there's a real, confirmed threat, not a theoretical one.
- Threat Center provides curated intelligence about active supply chain compromises, giving security teams clear context about what's actually being exploited in the wild versus what's merely a scored vulnerability. This helps teams focus their limited time on the threats that pose genuine business risk.
- Workflow Run Policies let organizations define and enforce security policies across all their GitHub Actions workflows, ensuring consistent security standards without requiring manual review of every workflow run.
- Dev Machine Guard reduces noise from the developer machine side with IDE Extension Governance, which tracks all installed extensions across VSCode and Cursor with comprehensive risk scores. Security teams can implement approved extension lists and automatic cooldown periods for new releases, proactively filtering out risky extensions rather than reacting to incidents after the fact. This is directly relevant given attacks like the NX Build System compromise, where a VSCode extension silently ran malicious code at activation. Instead of alerting on every extension update, Dev Machine Guard lets you enforce policy and focus attention on genuinely risky changes.
By focusing on confirmed threats and actual malicious behavior rather than raw CVSS scores, StepSecurity helps security teams cut through the noise and respond to what truly matters.
Why This Matters Now More Than Ever
The DevSecOps landscape is evolving rapidly. AI coding agents like GitHub Copilot, Claude Code, and Gemini CLI are accelerating development velocity, which means CI/CD pipelines are running more frequently, handling more sensitive operations, and integrating more third-party code than ever before. Every risk that Datadog identified in this report is amplified by this acceleration.
As Ashish noted, the foundational thinking that enabled early detection of the major 2025 compromises (understanding blast radius, monitoring runtime behavior, treating CI/CD as critical infrastructure) is precisely what organizations need to scale alongside AI-assisted development.
That's the approach we've built StepSecurity around. Harden-Runner, now trusted by over 10,000 repositories including projects from Microsoft, Google, and Kubernetes, provides the runtime security foundation. Combined with our GitHub Checks, Artifact Security suite, Orchestrate Security, and Maintained Actions, we offer the industry's most comprehensive platform for securing CI/CD pipelines against every category of risk that Datadog's report identifies.
Get Started
Every risk in the Datadog report has a corresponding mitigation in the StepSecurity platform. Here's where to begin:
- Pin all GitHub Actions to commit SHAs with Orchestrate Security or adopt StepSecurity Maintained Actions for critical workflows.
- Enable NPM Package Cooldown via GitHub Checks to stop day-of-release dependency risk.
- Activate NPM Package Compromised Updates as a required check to block known malicious packages before they enter your codebase.
- Add Harden-Runner to your workflows for runtime monitoring and egress control.
- Monitor your blast radius with NPM Package Search and the Threat Center.
We've been building for this moment. The data now agrees.
.png)