What we found
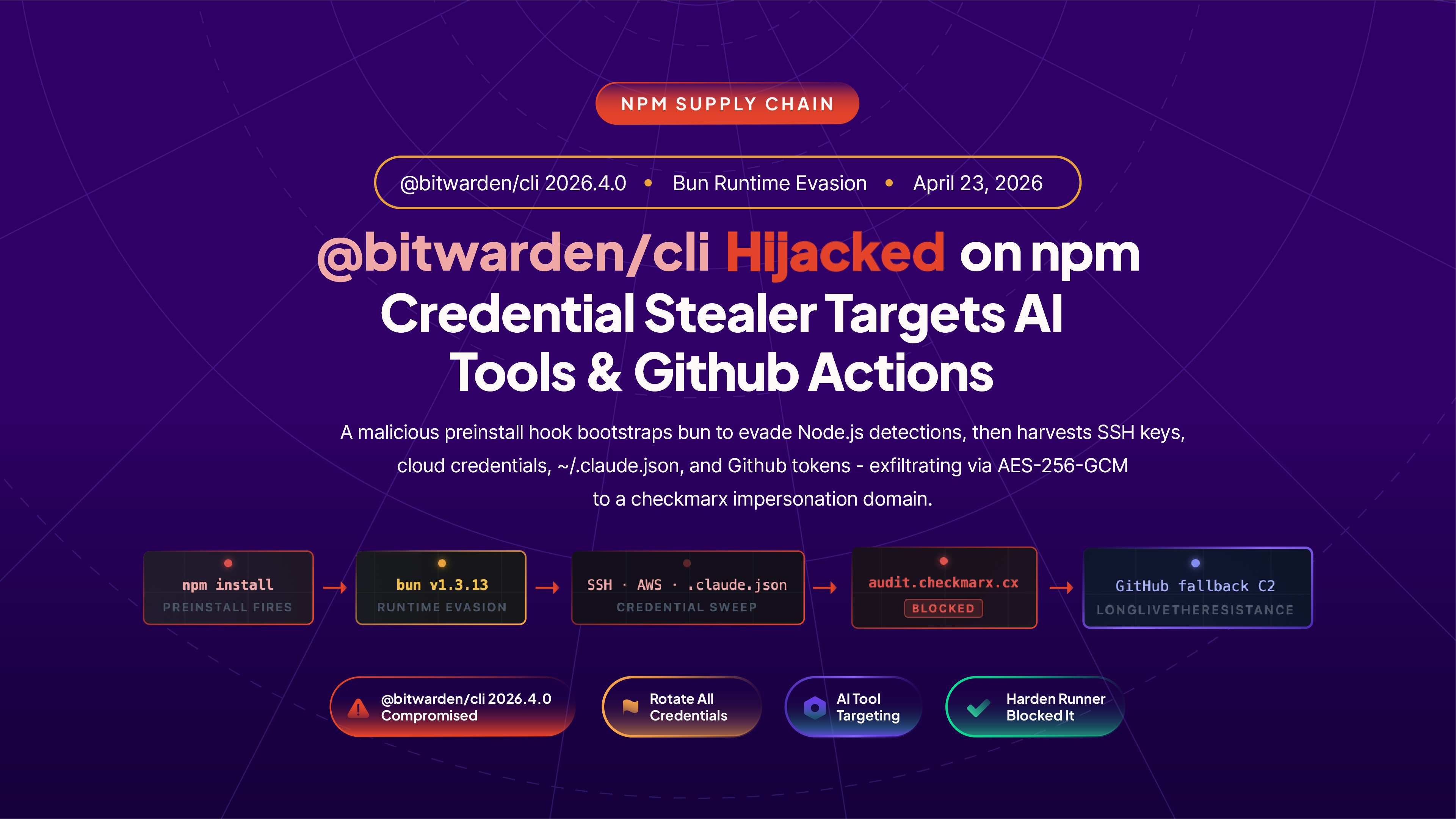
StepSecurity's OSS Package Security has flagged a coordinated npm supply chain attack reusing techniques reminiscent of the original Shai-Hulud campaign, but on a smaller scale and with a novel twist. Instead of relying on Node.js to execute its payload, the attacker downloads the Bun JavaScript runtime at install time and uses it to run a heavily obfuscated 11 MB script. This choice likely aims to evade detection tools focused on Node.js execution patterns. We have responsibly disclosed our findings to the maintainers of all affected packages.
Affected packages
The following packages have been confirmed compromised:
mbtv1.2.48, the npm wrapper for SAP's Cloud MTA Build Tool.@cap-js/sqlitev2.2.2, the SQLite adapter for the SAP Cloud Application Programming Model.- @cap-js/postgres
- @cap-js/db-service
Both packages are part of the broader SAP development ecosystem, which suggests the attacker is specifically targeting enterprise SAP developer environments. We are actively scanning for additional compromised packages and will update as our investigation continues.
How We Detected It
StepSecurity’s AI Package Analyst monitors every new npm publish in real time and compares each release against the package’s full version history. For mbt@1.2.48, three signals triggered an immediate CRITICAL verdict:
- A
preinstallscript appeared for the first time. Every prior release ofmbtused a standardinstallscript (node install cloud-mta-build-tool) to download the Go binary. Version 1.2.48 replaced this with"preinstall": "node setup.mjs"— a new file with no history in the package, firing before any install logic runs. - Two undocumented files introduced:
setup.mjsandexecution.js. Neither file exists in any prior release. The package jumped from 6 files (23 KB) to 10 files (11.7 MB). - Payload size anomaly. The package grew by a factor of 500 in a single version bump. The 11.6 MB
execution.jsis a single, newline-free obfuscated line — a strong structural indicator of a malicious payload, not a legitimate binary or asset.

Live Evidence: Victim Repositories Appearing on GitHub in Real Time
The repositories created by this malware carry a distinctive description hardcoded in the payload: “A Mini Shai-Hulud has Appeared”. At the time of writing, a public GitHub search for this string returns victim repositories being created in real time — each one representing a developer whose credentials were stolen during an mbt@1.2.48 install.

StepSecurity is actively investigating this alert. We will update this post with additional affected packages, indicators of compromise, deobfuscated payload analysis, and recommended remediation steps as our investigation progresses.